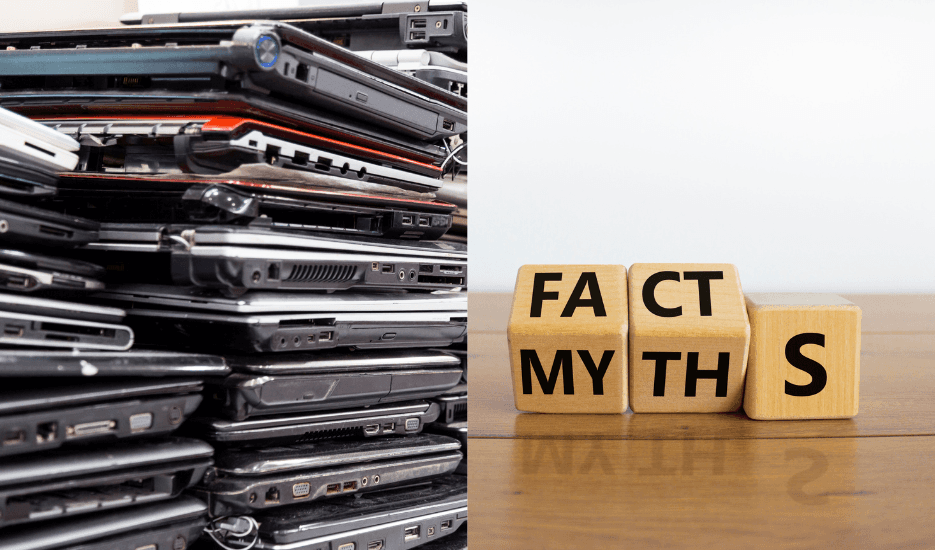
Second Thoughts on ITAD? Popular Myths Debunked
Second Thoughts on ITAD? Popular Myths Debunked
Apr 23, 2025
Explore the truth about asset value, compliance risks, and how smart IT asset disposal adds strategic value.
Explore the truth about asset value, compliance risks, and how smart IT asset disposal adds strategic value.
IT asset disposal (ITAD) is the process of disposing off assets that are no longer considered useful for an organisation. This is an integral part of IT asset management lifecycle, which helps organisations reduce maintenance costs, free up storage space, and avoid the potential risks associated with keeping obsolete or old assets.
However, despite its growing importance and relevance, ITAD is still surrounded by several misconceptions. Many businesses either overlook or delay disposing of their IT assets, primarily due to fear of data breaches & high costs or thinking that physical destruction of assets can suffice.
In this blog, let's uncover some of the most popular myths surrounding ITAD and set the record straight.
Why Do ITAD Myths Prevail
Even with businesses adopting advanced asset management systems and cyber security measures, asset disposal is often treated like an afterthought. This is partly because the risks involved in holding onto outdated assets are not visible until a compliance issue, data breach, or audit exposes the negligence.
Moreover, the general lack of awareness around data erasure and value recovery from the assets add to the confusion. Also, many small & medium enterprises (SMEs) believe that IT asset disposal is a complex and expensive process or that it is only relevant for large organisations with an expansive IT infrastructure.
Myth #1: Deleting/Formatting is Same as Data Erasure
One of the most common misconceptions businesses have about IT asset disposal is that simply deleting files or formatting drives is the same as data erasure.
Even after deleting files or formatting drives, widely accessible recovery software can easily retrieve business-sensitive data like client data, financial records and proprietary codes.
The only effective way to permanently remove data is through certified data erasure methods that are compliant with global and national standards. This ensures that the data is rendered unrecoverable.
Myth #2: E-Waste Recycling is the Same as ITAD
Despite their initial similarities, IT asset disposal is not the same as e-waste recycling. E-waste recycling focusses on recovering valuable metals and materials from old electronics.
IT asset disposal, on the contrary, involves secure data destruction, extending asset lifecycle through refurbishment and meeting compliance requirements like India's Digital Personal Data Protection Act 2023.
Myth #3 ITAD is Only for Large Businesses
It is very easy to assume that only organisations with a vast lineup of servers and a dedicated IT team will need IT asset disposal. However, small and medium entreprises (SMEs) are not less susceptible to environmental violations, non-compliance penalties and data breaches.
As a mattery of fact, because such organisations lack proper compliance and IT teams, they are even more exposed to such vulnerabilities compared to large ones.
Myth #4 Asset Destruction is the Most Secure Way
While this may be a correct statement and physical destruction of IT assets may be foolproof, it is not a cost effective solution for your business. Destruction or degaussing do remove data, but will also destroy the chance of recovering the asset value.
A better method for data destruction is secure data erasure, which uses dedicated equipment and software to desensitise the asset while keeping it functional.
Myth #5 We Don't Store Important Data on Old Devices
It feels good to believe that your old assets dont hold any sensitive or valuable data. In reality, however, your old devices often hold cached passwords, communication records and financial information. These may not be obvious, but are still at risk of breaches.
Legacy laptops, routers, servers and USB drives can be the gateway to data breaches. The cost of a breach, both from a reputational and financial standpoint, far outweighs the efforts required for secure and compliant IT asset disposal.
Final Thoughts
For far too long, ITAD has been treated as a back-office task, often rushed or neglected. However, in today's environment of ESG mandates, data security and evolving regulatory requirements, this is no longer a viable option.
Businesses now operate in an environment where every endpoint matters. Whether it's an out-of-use laptop, an outdated server or a rusty mobile phone lurking in the storage space, the risks in storing old IT assets are real.
For example, any data left behind on a drive, even unintentionally, can lead to reputational damage, regulatory violations or legal action. Thus, ITAD moves beyond just a logistics activity and becomes a necessity.
If your business is looking to move from a reactive ITAD process and adopt a compliant, secure and cost-effective approach to IT asset management, now is the time to act.
Explore how Recykal's end-to-end ITAD solution can help you manage risks, recover value, and build a future-ready asset lifecycle strategy. Contact us today.
IT asset disposal (ITAD) is the process of disposing off assets that are no longer considered useful for an organisation. This is an integral part of IT asset management lifecycle, which helps organisations reduce maintenance costs, free up storage space, and avoid the potential risks associated with keeping obsolete or old assets.
However, despite its growing importance and relevance, ITAD is still surrounded by several misconceptions. Many businesses either overlook or delay disposing of their IT assets, primarily due to fear of data breaches & high costs or thinking that physical destruction of assets can suffice.
In this blog, let's uncover some of the most popular myths surrounding ITAD and set the record straight.
Why Do ITAD Myths Prevail
Even with businesses adopting advanced asset management systems and cyber security measures, asset disposal is often treated like an afterthought. This is partly because the risks involved in holding onto outdated assets are not visible until a compliance issue, data breach, or audit exposes the negligence.
Moreover, the general lack of awareness around data erasure and value recovery from the assets add to the confusion. Also, many small & medium enterprises (SMEs) believe that IT asset disposal is a complex and expensive process or that it is only relevant for large organisations with an expansive IT infrastructure.
Myth #1: Deleting/Formatting is Same as Data Erasure
One of the most common misconceptions businesses have about IT asset disposal is that simply deleting files or formatting drives is the same as data erasure.
Even after deleting files or formatting drives, widely accessible recovery software can easily retrieve business-sensitive data like client data, financial records and proprietary codes.
The only effective way to permanently remove data is through certified data erasure methods that are compliant with global and national standards. This ensures that the data is rendered unrecoverable.
Myth #2: E-Waste Recycling is the Same as ITAD
Despite their initial similarities, IT asset disposal is not the same as e-waste recycling. E-waste recycling focusses on recovering valuable metals and materials from old electronics.
IT asset disposal, on the contrary, involves secure data destruction, extending asset lifecycle through refurbishment and meeting compliance requirements like India's Digital Personal Data Protection Act 2023.
Myth #3 ITAD is Only for Large Businesses
It is very easy to assume that only organisations with a vast lineup of servers and a dedicated IT team will need IT asset disposal. However, small and medium entreprises (SMEs) are not less susceptible to environmental violations, non-compliance penalties and data breaches.
As a mattery of fact, because such organisations lack proper compliance and IT teams, they are even more exposed to such vulnerabilities compared to large ones.
Myth #4 Asset Destruction is the Most Secure Way
While this may be a correct statement and physical destruction of IT assets may be foolproof, it is not a cost effective solution for your business. Destruction or degaussing do remove data, but will also destroy the chance of recovering the asset value.
A better method for data destruction is secure data erasure, which uses dedicated equipment and software to desensitise the asset while keeping it functional.
Myth #5 We Don't Store Important Data on Old Devices
It feels good to believe that your old assets dont hold any sensitive or valuable data. In reality, however, your old devices often hold cached passwords, communication records and financial information. These may not be obvious, but are still at risk of breaches.
Legacy laptops, routers, servers and USB drives can be the gateway to data breaches. The cost of a breach, both from a reputational and financial standpoint, far outweighs the efforts required for secure and compliant IT asset disposal.
Final Thoughts
For far too long, ITAD has been treated as a back-office task, often rushed or neglected. However, in today's environment of ESG mandates, data security and evolving regulatory requirements, this is no longer a viable option.
Businesses now operate in an environment where every endpoint matters. Whether it's an out-of-use laptop, an outdated server or a rusty mobile phone lurking in the storage space, the risks in storing old IT assets are real.
For example, any data left behind on a drive, even unintentionally, can lead to reputational damage, regulatory violations or legal action. Thus, ITAD moves beyond just a logistics activity and becomes a necessity.
If your business is looking to move from a reactive ITAD process and adopt a compliant, secure and cost-effective approach to IT asset management, now is the time to act.
Explore how Recykal's end-to-end ITAD solution can help you manage risks, recover value, and build a future-ready asset lifecycle strategy. Contact us today.
Related Blogs
Read More From Our Blog
Read More From Our Blog
Join our newsletter list
Sign up to get the most recent blog articles in your email every week.